LastPass has confirmed that their customers’ password vaults, which store passwords and other secrets, have been compromised in a data breach.
The intruders acquired a backup of the encrypted customer vault data by using cloud storage keys stolen from a LastPass employee.
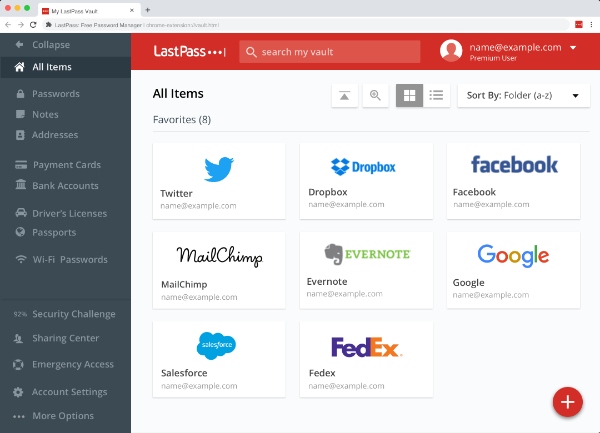
The cache of password vaults is in a proprietary binary format that comprises both unencrypted and encrypted data, though the specifics of the format were not disclosed. Unencrypted information includes web addresses stored in the vault, however, there is no information on when the backup was taken.
LastPass has warned that the hackers who perpetrated the attack may try to use brute force to crack their customers’ master passwords and decrypt their copy of the vault data. This could put sensitive information such as names, email addresses, phone numbers and billing information at risk.
The company has urged customers to use a strong, complex, unique password to protect their vault. By doing so, customers can ensure that their data remain secure even if the hackers can decrypt the vault.
In this instance, if a malicious actor can access customers’ encrypted password vaults, they would only need the master password to unlock them. Consequently, it is important to ensure that your LastPass vault is secure.
To do so, change the master password to a unique and complex one, and store it in a safe place.
Additionally, you should change the passwords in your LastPass vault, starting with the most crucial accounts, such as your email, phone plan, bank and social media accounts, and then proceeding to the rest of them.
Two-factor authentication makes it much harder for an attacker to access your accounts without the second layer of protection; for example, a phone pop-up, a texted code, or an emailed code. It is important to prioritize the security of those accounts which require two-factor authentication, such as email and cell phone plans.